The reasons why it is so important to detect services and software version on the target device is because some services share the same ports, therefore in order to discriminate services, detecting the software running behind the port may become critical.
Yet, the main reason most sysadmins will run a version scan is to detect security holes or vulnerabilities belonging to outdated or specific software versions.
A regular Nmap scan can reveal opened ports, by default it won’t show you services behind it, you can see a 80 port opened, yet you may need to know if Apache, Nginx or IIS is listening.
By adding version detection NSE (Nmap Scripting Engine) can also contrast the identified software with vulnerabilities databases (see “How to use Vuls”).
How Nmap services and version detection works?
In order to detect services Nmap uses the database called nmap-services including possible services per port, the list can be found at https://svn.nmap.org/nmap/nmap-services, if you have a customized port configuration you can edit the file located at /usr/share/nmap/nmap-services. To enable service detection the flag -A is used.
To detect software versions Nmap has another database called nmap-service-probes which includes probes for querying and match expressions to identify responses.
Both databases help Nmap first to detect the service behind the port such as ssh or http. Second, Nmap will try to find the software providing the service (such as OpenSSH for ssh or Nginx or Apache for http) and the specific version number.
In order to increase version detection accuracy, this specific scan integrates NSE (Nmap Scripting Engine) to launch scripts against suspected services to confirm or discard detections.
You can always regulate the intensity of a scan as will be explained below despite it will be only useful against uncommon services on targets.
Getting started with Nmap Services and Version Detection:
To install Nmap on Debian and based Linux distributions run:
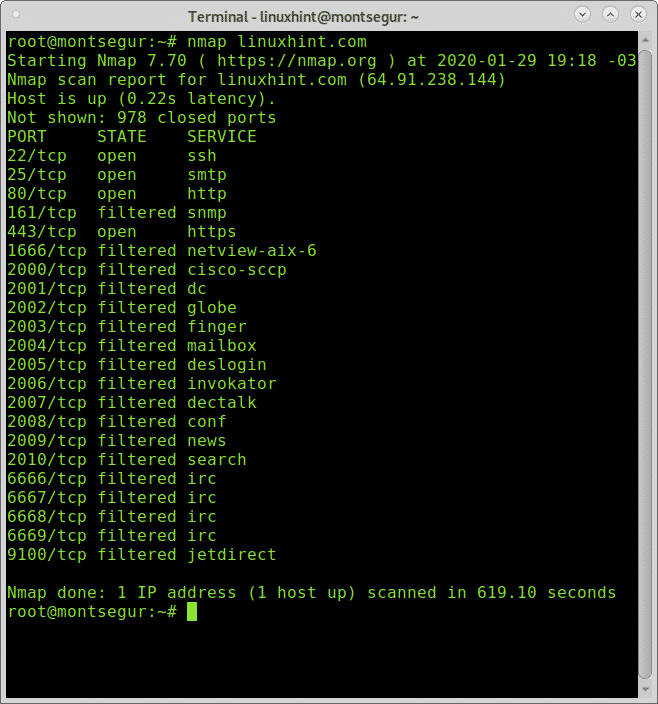
Before starting lets run a regular Nmap scan by executing:
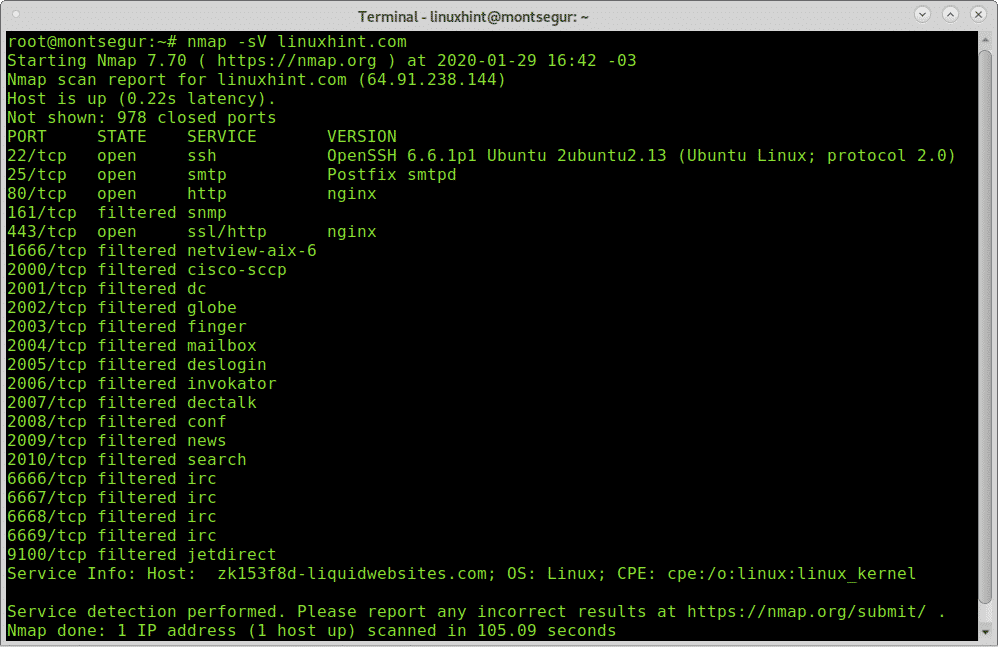
You can see open and filtered ports are listed, now lets run a version scan by executing:
You can see in the output above this time Nmap detected OpenSSH 6.6.1p1 behind port 22, Postfix behind port 25 and Nginx behind ports 80 and 443. In some cases, Nmap cannot distinguish filtered ports, in such cases Nmap will mark them as filtered, yet if instructed it will continue probes against these ports.
It is possible to determine que grade of intensity Nmap will use to detect software versions, by default the level 7 and the possible range is from 0 to 9. This feature will only show results if uncommon services are running on the target, there will not be differences in servers with widely used services. The following example shows a version scan with minimal intensity:
To run the most aggressive version detection scan, replace the 0 for 9:
The level 9 can be also executed as:
For a low intensity version detection (2) you can use:
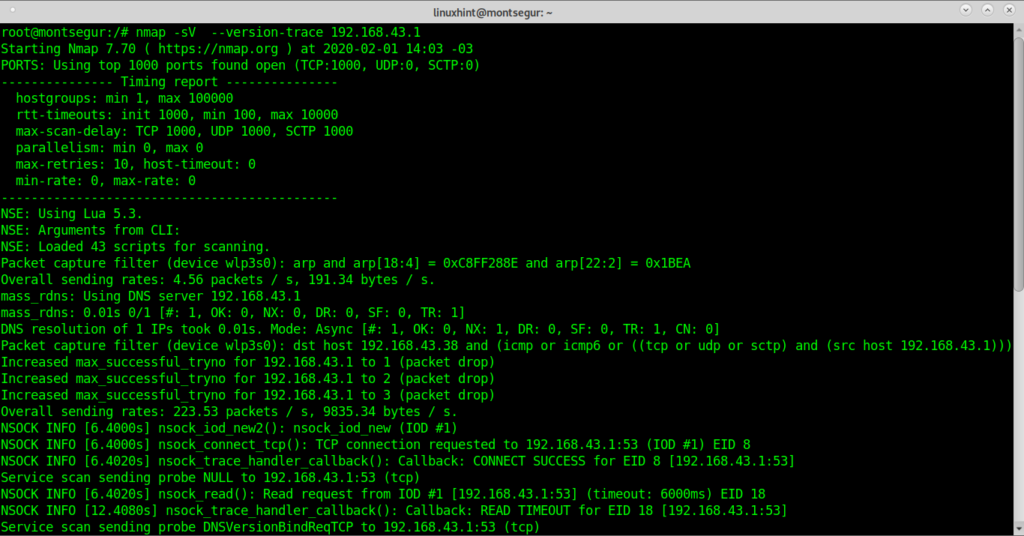
You can instruct Nmap to show the whole process by adding the –version-trace option:
Now, let’s use the flag -A which also enables version detection, additionally to OS, traceroute and NSE:
As you can see after the scan NSE post scan as launched detecting possible vulnerabilities for the exposed Bind version.
The device type and OS were successfully detected as phone and Android and a traceroute was also executed (the Android mobile is working as hotspot).
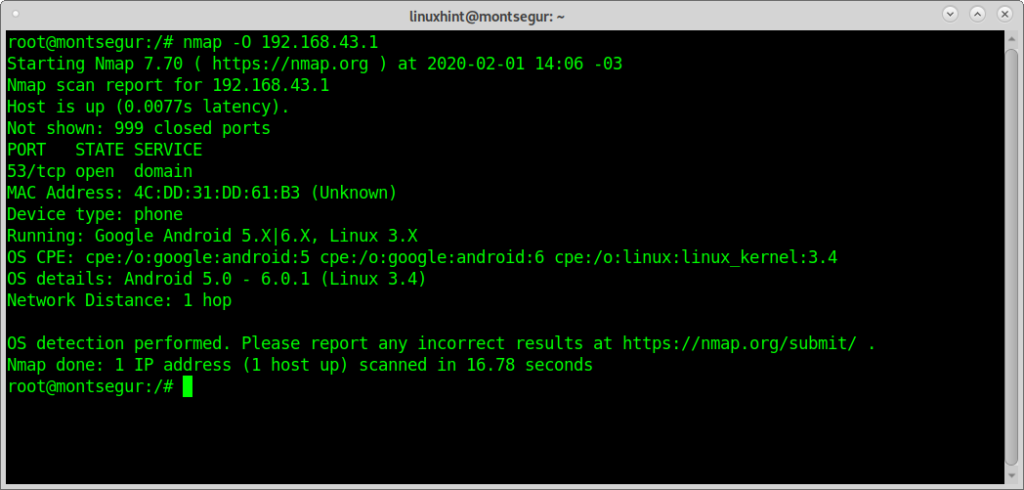
While in order to detect services NSE is integrated to allow a better accuracy, a specific OS detection scan can be launched with the -O flag as in the following example:
As you see the result was pretty similar without NSE, which is by default integrated to version probes.
As you could see, with Nmap and few commands you’ll be able to learn relevant information on software running on targets, if the flag -A is enabled Nmap will test results trying to find security holes for the specified service versions.
I hope you found this tutorial on Nmap Version Scan useful, there are a lot of additional high quality content on Nmap at https://linuxhint.com/?s=nmap.
Keep following LinuxHint for more tips and updates on Linux and networking.